
You never throw incompatible cargo together arbitrarily. You wouldn’t mix food and fuel in the same container. You wouldn’t co-mingle delicate electronics and heavy steel plates.
Just like you separate your physical cargo, keeping ship data secure also requires some judicious separation. Many of the recent news stories about the cybersecurity weaknesses of marine electronics have a common underlying pattern: systems interconnected without proper attention to separating the electronic “cargo” are vulnerable to attack.
To be clear, I am not a marine electronics expert. However, my company has experience in similar areas and we may have some interesting ideas and technology for this industry to consider when it comes to cybersecurity and trusted computing. A number of the technology trends related to cybersecurity that we have seen in other transportation industries (e.g., aerospace and land vehicles) are appearing in marine electronics: rising concern about hacking, increased functionality consolidated into fewer but more powerful computers, and more internal and external interconnectivity. In the face of these trends, customers have a fundamental need to trust the onboard technology. Trust in electronics systems is built on three pillars:
In this blog I’ll focus on isolation, with later blogs on the other two pillars. Isolation is a computer software technique that is analogous to the physical separation of cargo, keeping things separate that could harm one another if mixed.
Also known as separation or partitioning, isolation is a means of supporting multiple software applications running on one computer hardware platform while also preventing any unwanted interaction between them. For example, you wouldn’t want a video game app used for entertainment to influence a GPS location app used for navigation. If those two apps are running on the same computer hardware, or even indirectly interconnected by the ship’s networks, then there is the possibility for unwanted interaction.

In order to rely on our marine electronics, we must examine every point in the system where software apps might interact, implementing some type of isolation. If we don’t, we cannot fully trust the system because we cannot guarantee there won’t be unforeseen and undesirable interactions.
There are several choices for isolation. Physical separation is the traditional form of isolation, segregating each software function to its own computer hardware and then avoiding any interconnection between those computers. However, this is costly, bulky, and difficult to upgrade. Thus, the trend in other industries has been to consolidate both existing and new electronics functionality into a single, smaller, easier-to-maintain unit. In this case, instead of physical separation, we must use electronic or virtual methods to isolate the functions that should not interact with each other yet are running on the same underlying computing and communication hardware.
Most modern operating systems provide at least a modicum of isolation. The most popular Operating System (OS) in the world, Microsoft Windows, makes a reasonable attempt to play referee between the applications it hosts. For example, a glitch in your Excel spreadsheet in one window should not affect the audio playing from your music app in another window. However, for performance and flexibility reasons, desktop operating systems like Windows, Linux, or Mac OS do not rigorously separate software applications. Thus, occasionally a problem in one application can cause other applications to slow, or in rare instances, the entire system freezes. This type of unwanted interaction might be simply an annoyance on your personal laptop, but it could be a significant or even life-threatening problem on a shipboard system.
That’s a problem!
Many embedded electronic systems are not complex enough to need an operating system, but if they do, rather than relying on the relatively weak separation of a desktop OS, the traditional choice has been a Real Time Operating System (RTOS), such as Wind River VxWorks or FreeRTOS. When related applications are hosted by an RTOS, this is a reasonable approach. However, as we continue to see more and more consolidation of functionality, the same computer may now host unrelated applications – and now isolation provided by an RTOS is probably not sufficient.
 Source: Pixnio
Source: PixnioWe need isolation that is analogous to separate holds in the ship that are separated by cold, hard steel. The isolation must be impermeable, so nothing can leak between holds. In the computing world we call this level of isolation virtualization, implemented by a hypervisor. The hypervisor leverages special processor hardware to enforce rigorous separation of software so that one application cannot negatively impact the performance of another application. In fact, each application has the illusion that it is the only software running on the processor, when in reality, the hypervisor is juggling several different applications, each in its own virtual machine. This technique is so powerful, that one can even run multiple operating systems on the same processor, such as Windows and Linux at the same time, each isolated from the other.
Using virtualization, we can consolidate multiple ship functions on a single processor, yet keep them isolated from one another to prevent unwanted interaction. A variety of instrumentation and navigation software that was formerly federated (each on its own box, perhaps connected by an NMEA 2000 or SeaTalk bus) can now be integrated on a single machine. In the aerospace industry, this technique is called Integrated Modular Avionics.
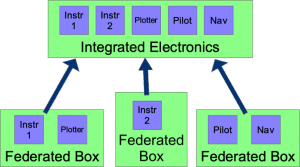
A similar approach could be adopted to integrate marine electronics.
Consolidation drastically reduces the amount of necessary wiring and rack space while providing equal or better functionality. Updates and upgrades are also much easier. Safe interconnectivity is also now possible, allowing mobile devices access to appropriate functionality while isolating critical functions to separate and secure virtual machines.
Isolation of software functionality via virtualization can improve the reliability and security of marine electronics. However, isolation is not the complete story for trusted computing. There is also assurance and monitoring to consider.